第四届“长城杯”网络安全大赛暨京津冀网络安全技能竞赛(初赛)WP

easyre
每一位和下一位异或
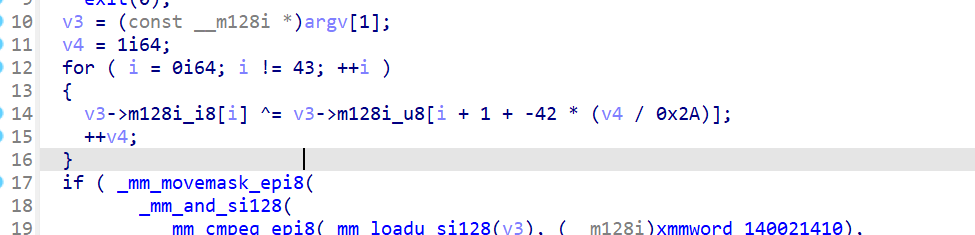
1 | data=[ 0x0A, 0x0D, 0x06, 0x1C, 0x1D, 0x05, 0x05, 0x5F, 0x0D, 0x03, |
flag{fcf94739-da66-467c-a77f-b50d12a67437}
tmaze
迷宫,应该是个图
找到起点和终点
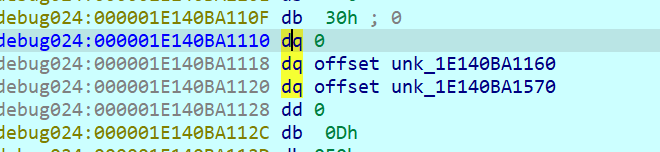
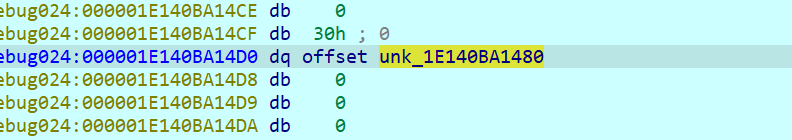
然后直接idapython递归爆破就行
1 | from ida_bytes import * |
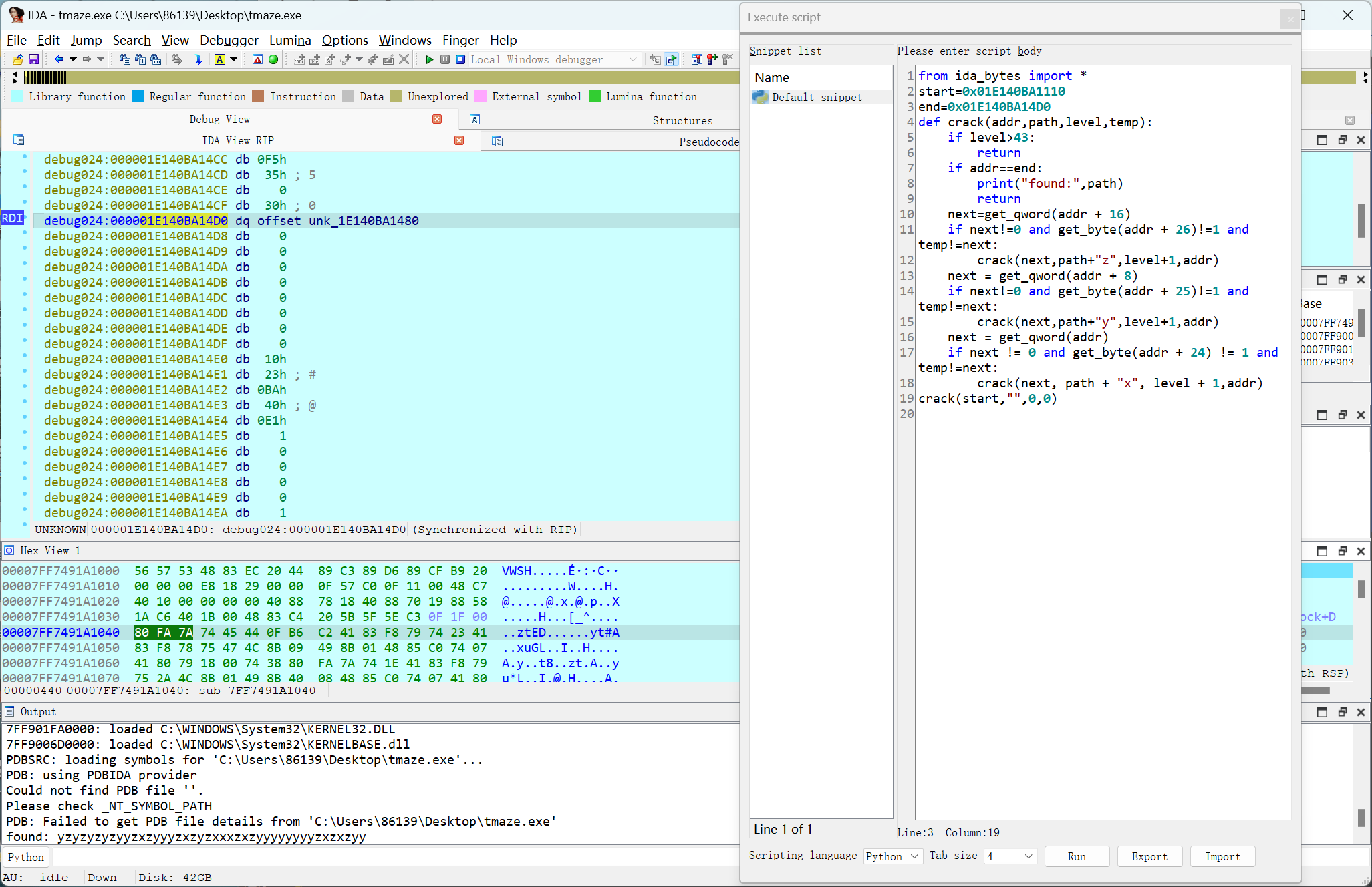
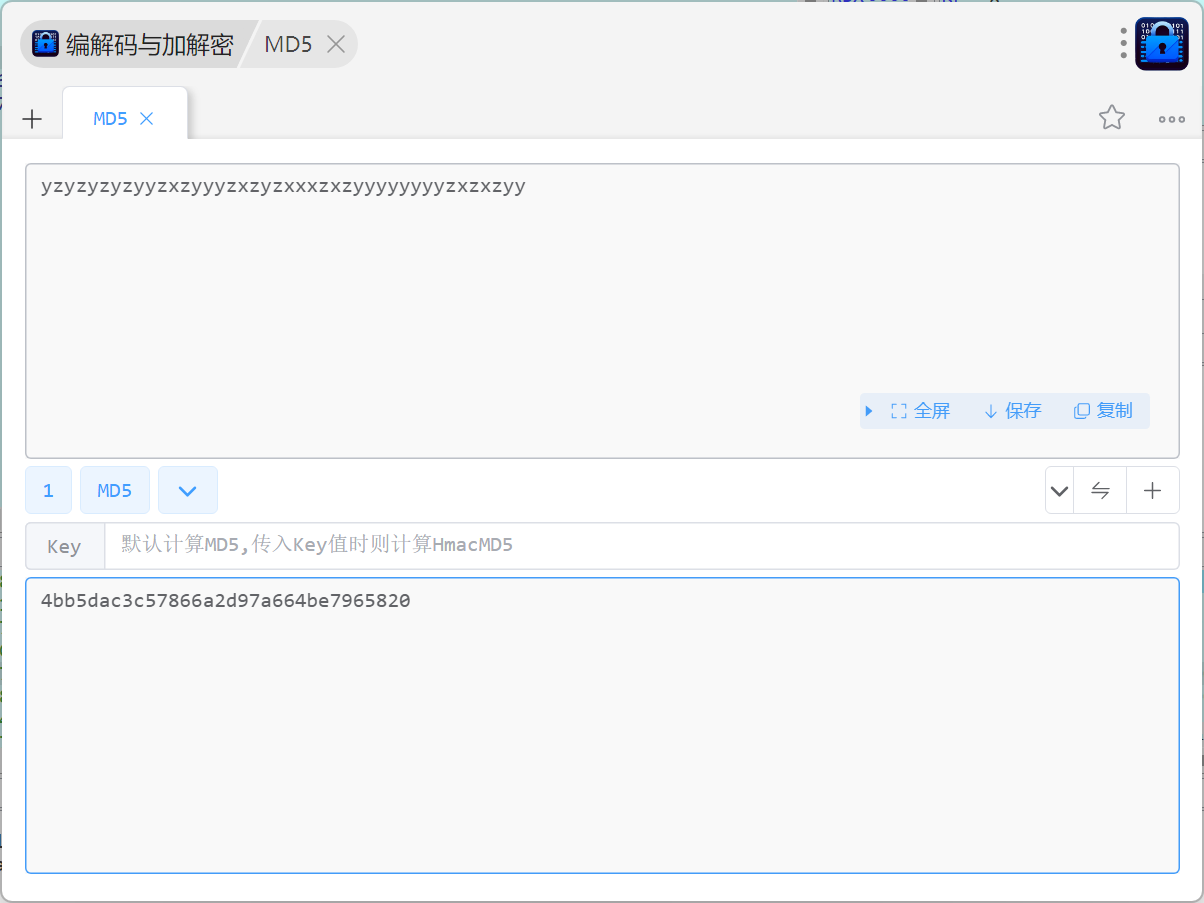
flag{4bb5dac3-c578-66a2-d97a-664be7965820}
- Title: 第四届“长城杯”网络安全大赛暨京津冀网络安全技能竞赛(初赛)WP
- Author: clev1L
- Created at : 2024-09-08 15:50:49
- Updated at : 2025-04-07 14:29:29
- Link: https://github.com/clev1l/2024/09/08/第四届“长城杯”网络安全大赛暨京津冀网络安全技能竞赛(初赛)WP/
- License: This work is licensed under CC BY-NC-SA 4.0.
Comments