NepCTF2024 WP

OezAndroid
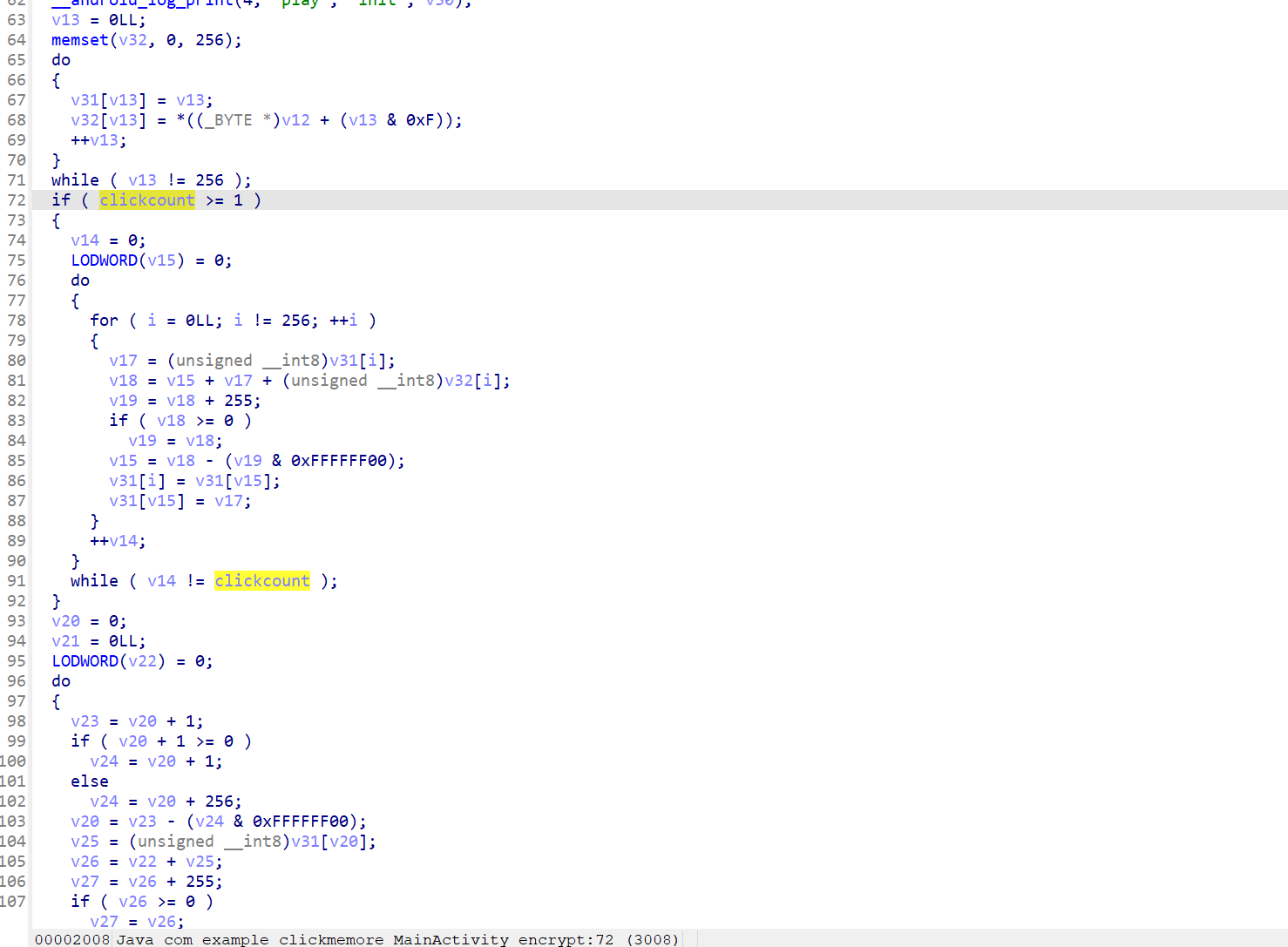
点击次数对应s盒混淆次数,直接爆破
1 | #include <stdio.h> |
爆出来count为10714
这里有个这玩意,会导致点击就闪退,拿出mt管理器给他删了就行
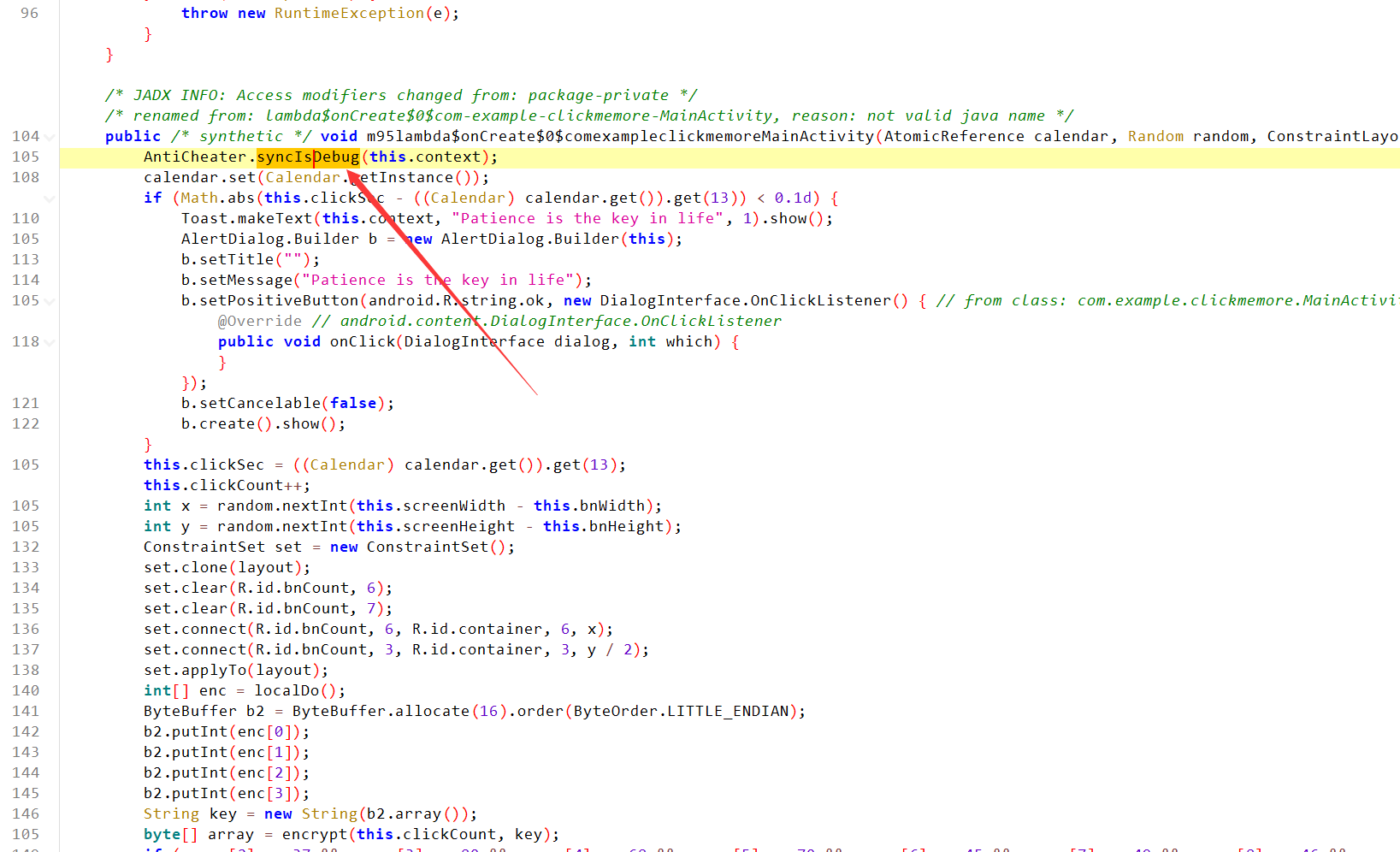
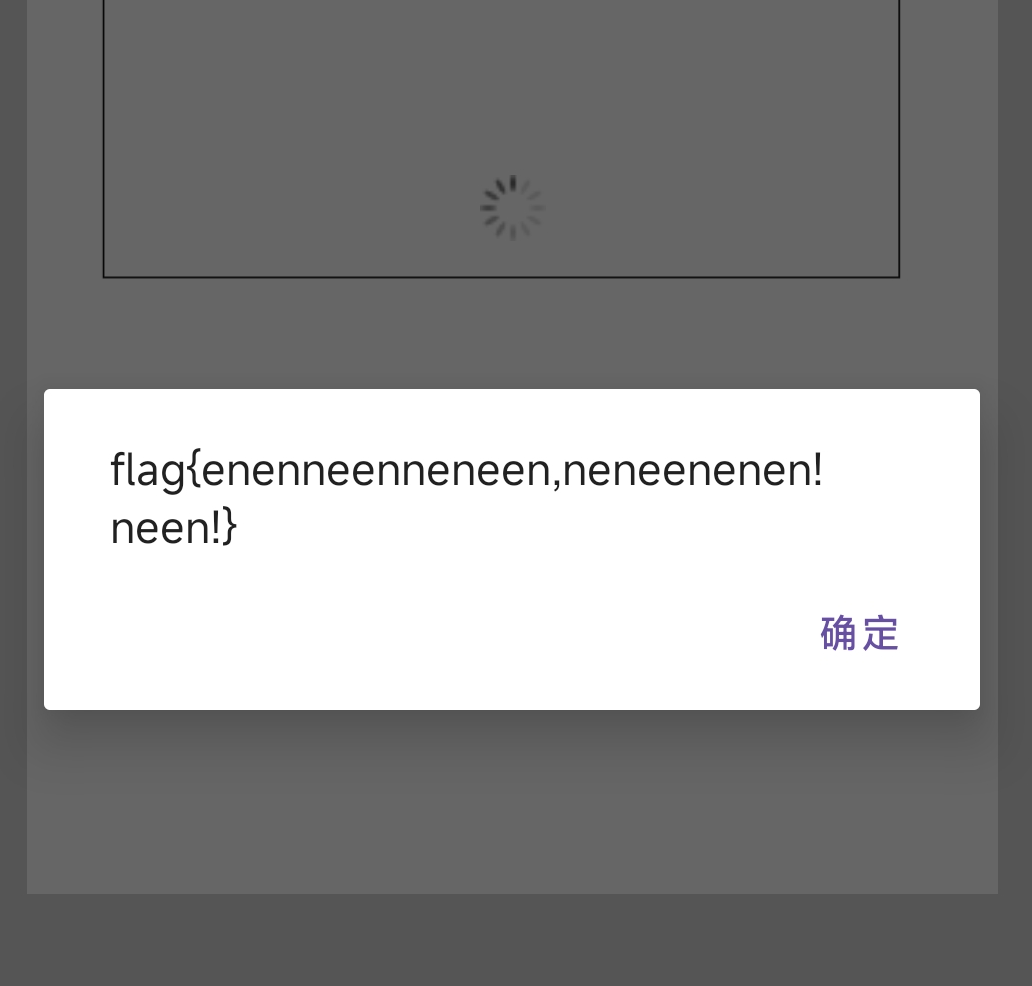
然后frida hook encrypt,将传入的参数改成10714,点击确认就能拿到flag
1 | function hook() |
ezAndroid
主要逻辑在so层,去个花
复现出算法
1 | from ctypes import * |
然后z3求解就行
1 | from z3 import * |
easyobf
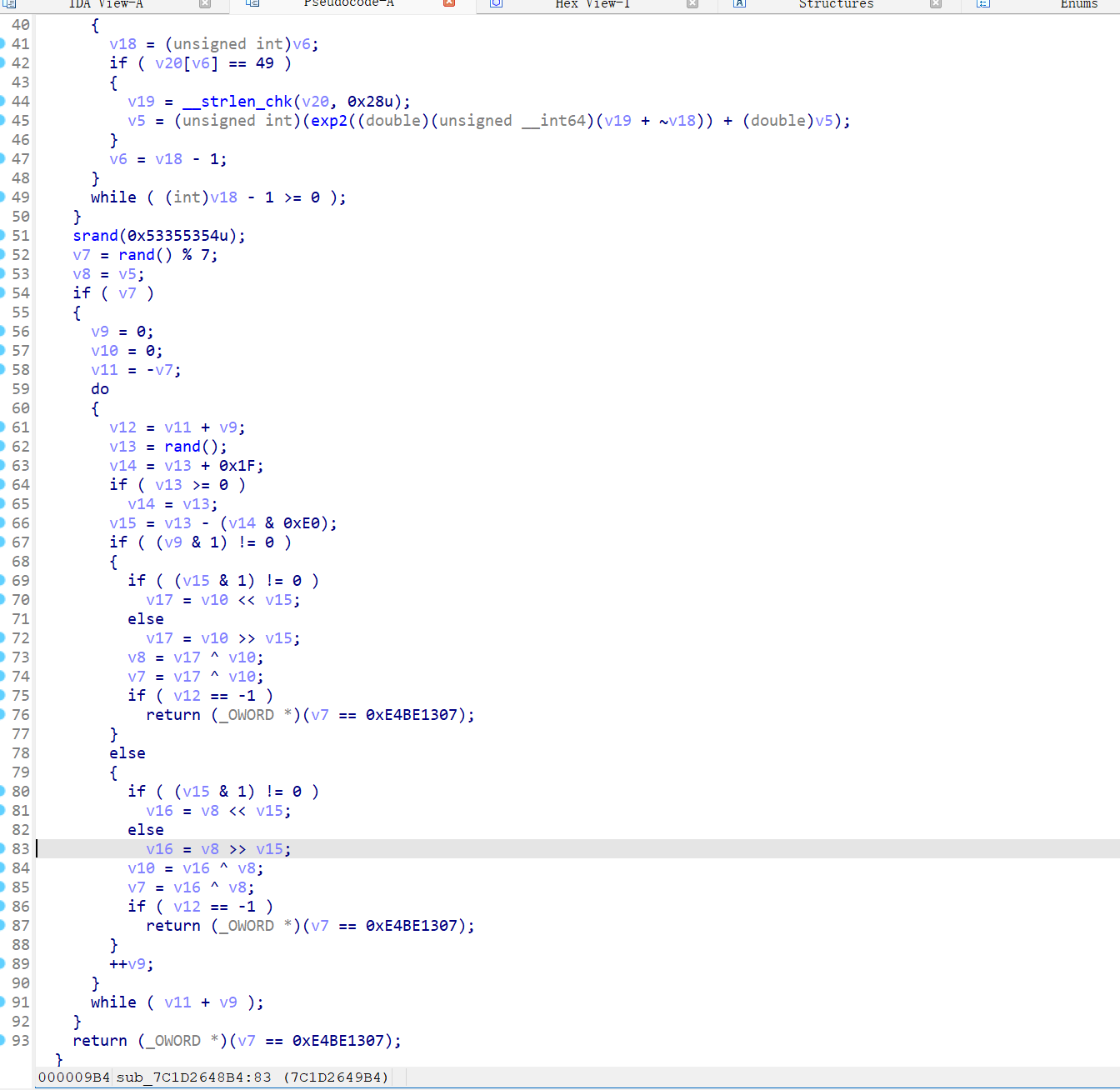
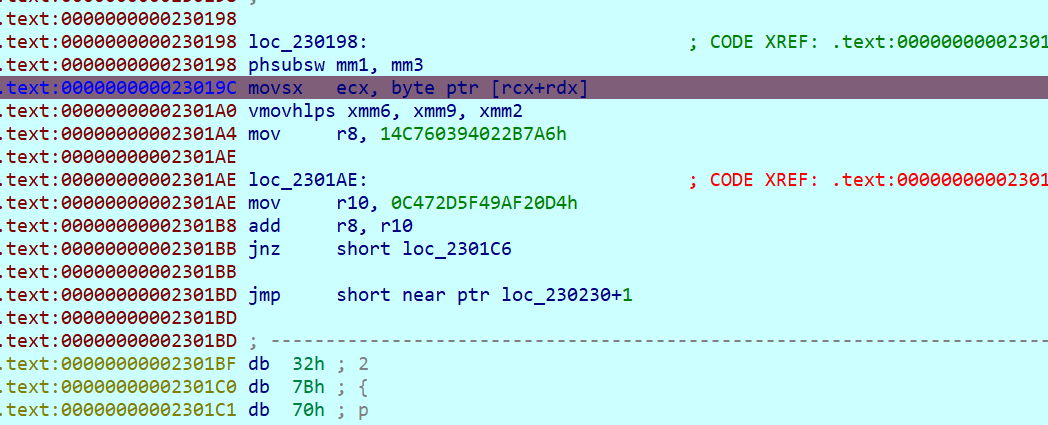
不会去混淆,只能硬撕汇编
跟到这开始加密了
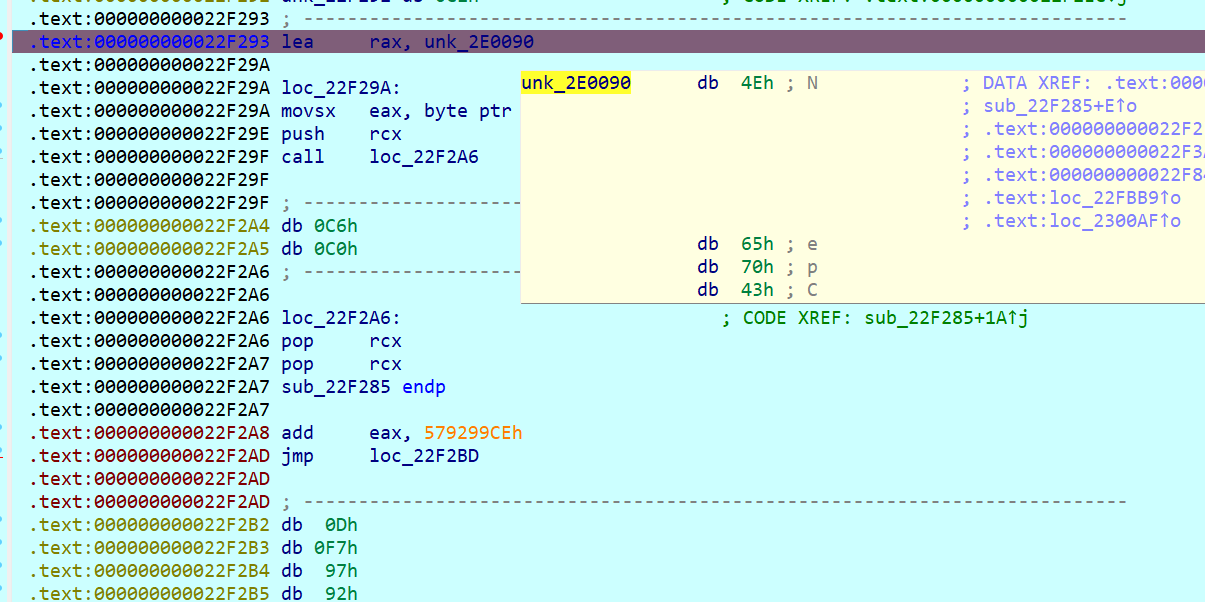
开始抄汇编
1 | test=ord(j) |
在这拿到密文
发现爆破出来答案不对,猜了一下发现差了个^i,应该是有反调试我没跟到吧,汗流浃背了
1 | from string import printable |
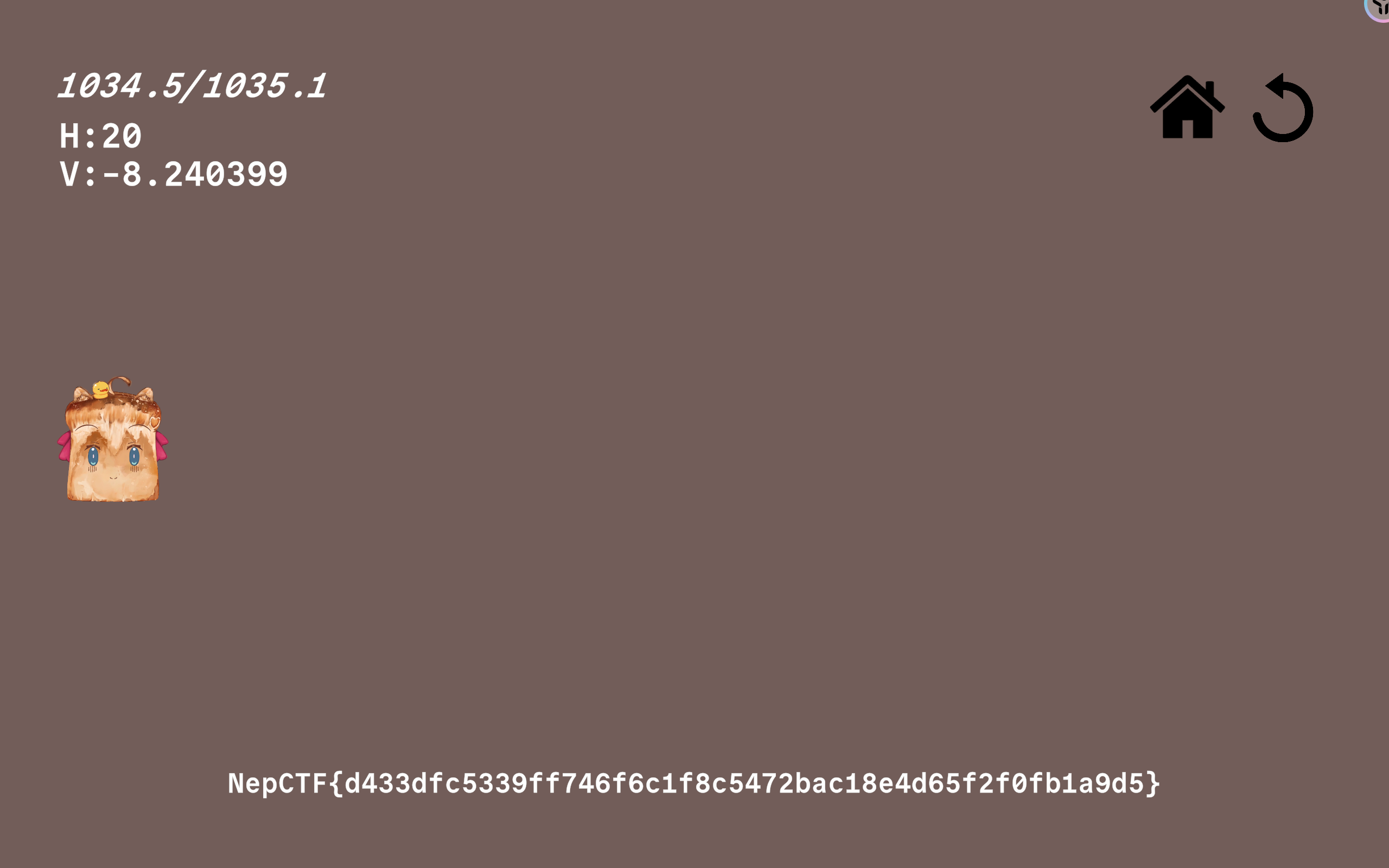
Super Neuro : Escape from Flame!
玩一玩,发现能贴墙飞(贴着墙,一直按方向键,然后连点空格),但是经常有障碍物给我卡着
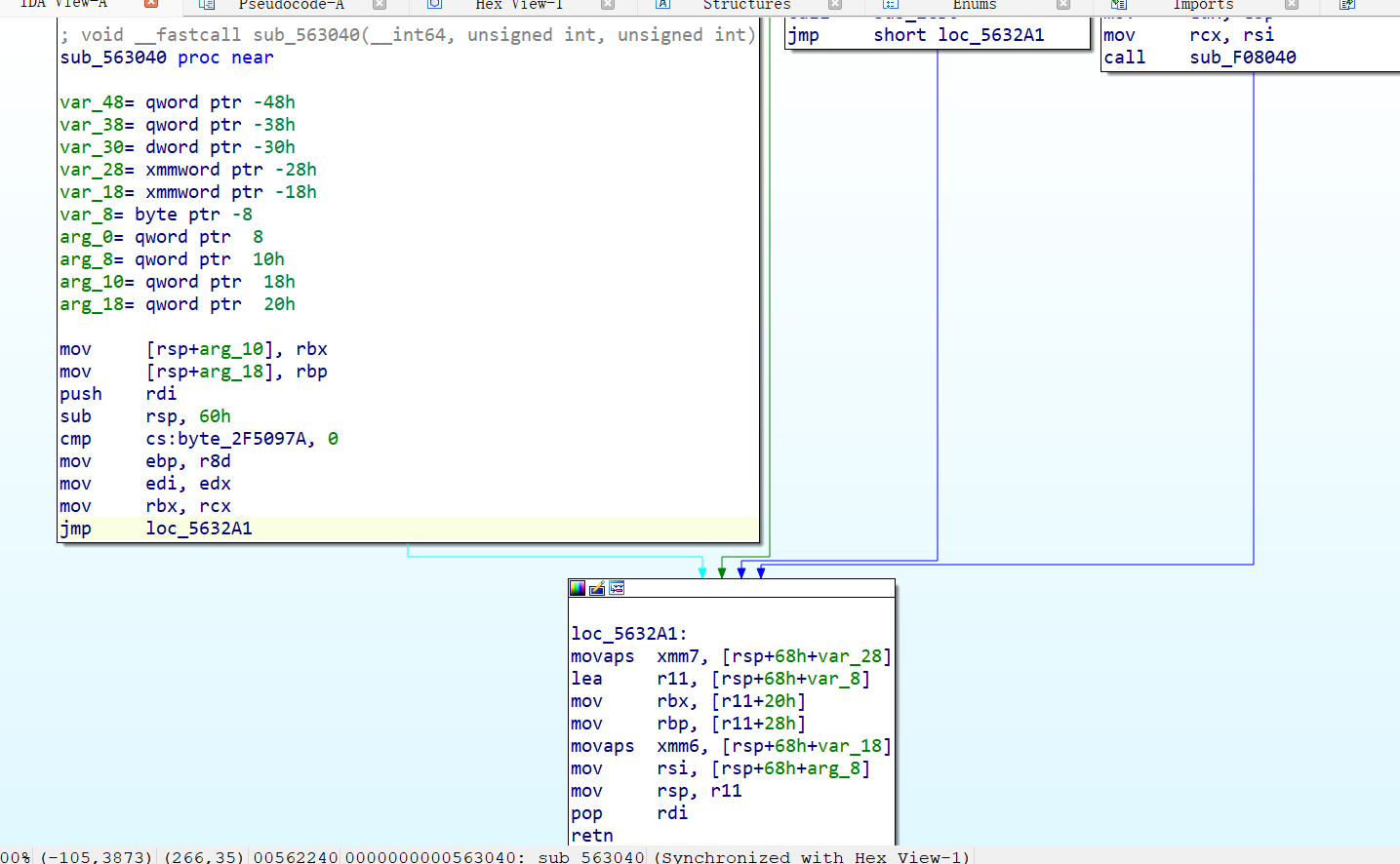
Il2CppDumper后看看函数,这个应该就是生成那些平台的
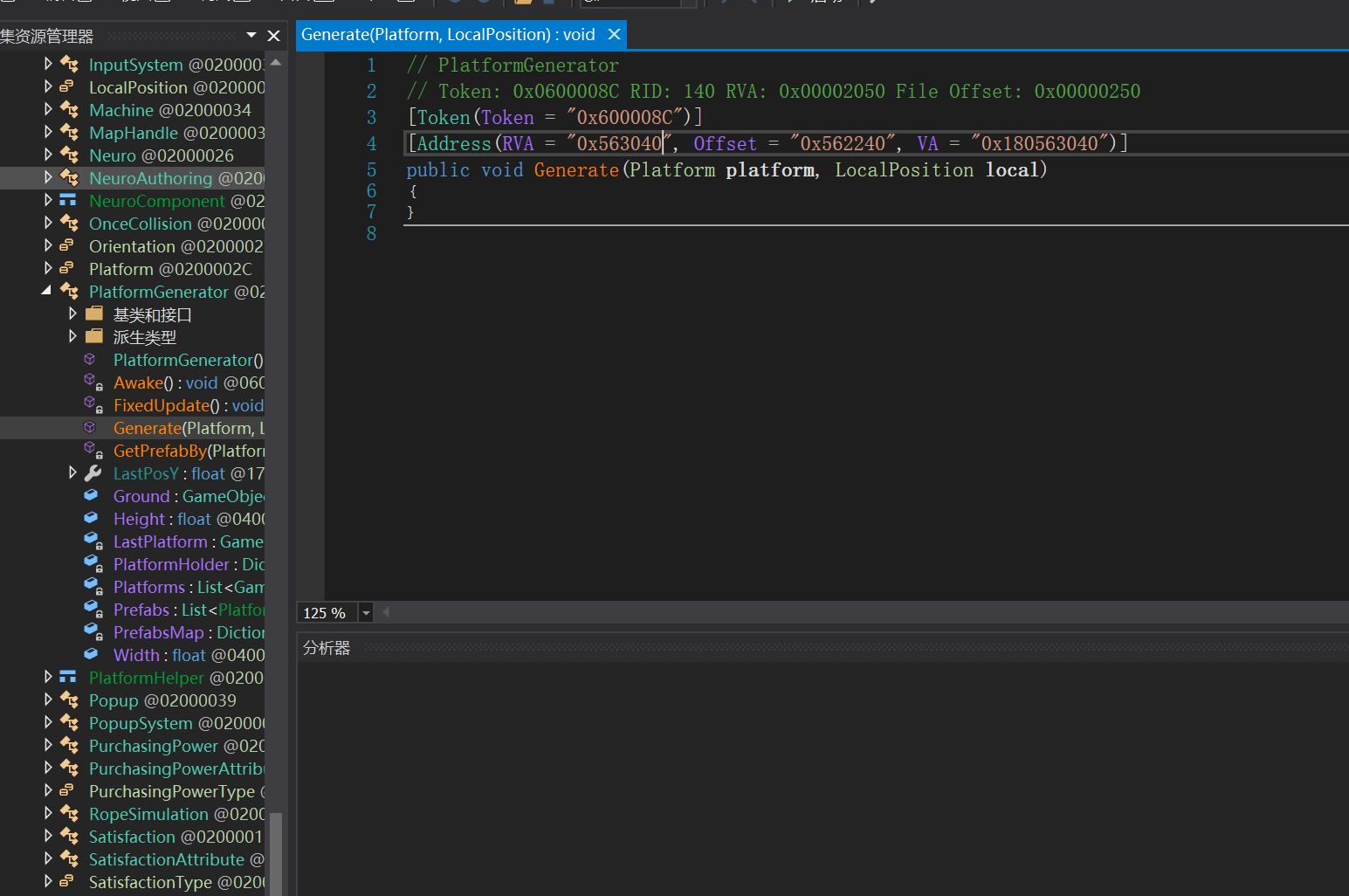
直接ida给他ret了,然后平台就没了,然后就可以贴墙起飞了
- Title: NepCTF2024 WP
- Author: clev1L
- Created at : 2024-08-26 10:12:45
- Updated at : 2025-04-07 14:29:29
- Link: https://github.com/clev1l/2024/08/26/NepCTF2024-WP/
- License: This work is licensed under CC BY-NC-SA 4.0.
Comments